A hyperactive LockBit group led to an increase in ransomware campaigns in the final quarter of 2023, according to XDR security vendor ReliaQuest.
In his Ransomware Trends in Q4 2023 report, ReliaQuest found that ransomware activity increased by 80% between October and December 2023 compared to the same period in 2022.
During this period, a total of 1,262 victims were recorded on the data breach sites, from multiple industries including manufacturing, construction, professional, scientific and technical services.
LockBit dominates the threat landscape
LockBit was the most active threat group, with 275 victims listed on data leak sites during the study period.
This represents more than twice the number of reported victims compared to the second most active group, Playwhich resulted in 110 victims on data leak sites in the fourth quarter of 2023. ALPHV/BlackCat came third with 102 claimed victims, NoEscape came fourth (76), and 8Base came fifth (75).
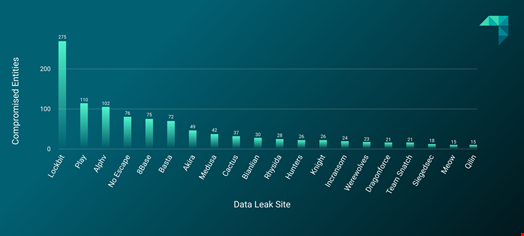
This dominance aligns with previous trends as LockBit was the most active group throughout 2023.
ReliaQuest observed that LockBitSupp, the group’s public representative, had consistently attempted to recruit members of No leak and ALPHV, whose activity was disrupted by law enforcement operations.
Read more: Law enforcement confirms BlackCat removal and decryption key offered to victims
For example, LockBitSupp was observed offering use of LockBit’s data leak site and trading panel to affiliates of both groups.
“It is unclear whether the recruitment program worked, but at least one organization whose compromise was linked to ALPHV ended up being named on the LockBit leak site,” the ReliaQuest report notes.
Meanwhile, ransomware groups NoEscape and Play appear to have increased their activity in the final quarter of 2023.
Citrix is bleeding, MOVEit down
In November, the number of ransomware victim claims increased, with 484 this month alone.
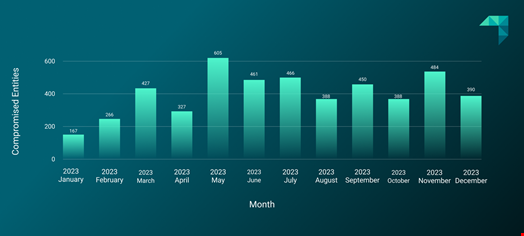
ReliaQuest attributed this spike to increased exploitation of the Citrix Bleed vulnerability, which was primarily exploited by LockBit affiliates.
“On top of that, November brought new, aggressive extortion tactics from the ALPHV ransomware group, involving the U.S. Securities and Exchange Commission (SEC) to pressure their targets,” the report said.
However, the MOVEit campaign appears to have calmed down, with the Clop Group citing 95.3% fewer victims in the fourth quarter of 2023 compared to the previous quarter.
Read more: MOVEit Exploitation Fallout Generates Record Ransomware Attacks
Tactical Ransomware Group Predictions for 2024
Based on its data, ReliaQuest expects the increase in ransomware claims to continue in 2024.
The company also shared its 2024 predictions regarding the tactics of some of the most active ransomware groups.
These include:
- LockBit NetScaler Affinity: LockBit exploits vulnerabilities in NetScaler, a widely used networking technology, to target high-value organizations (banks, governments, law firms, etc.). Given the profitability and success of these attacks, ReliaQuest believes that LockBit will likely continue its exploitation of NetScaler and its focus on the industry.
- Clop’s comeback potential: Although Clop’s activity declined towards the end of 2023, ReliaQuest expects the group to “make a comeback” in 2024. “This slowdown after a strong increase in activity has already been observed with Clop, at the continuation of a 2020-21 campaign that abused several zero-days. “, we read in the report.
- Silent threat of NoEscape (for now): Although NoEscape appears to have disappeared, after shutting down its data leak site for example, ReliaQuest has stated that it will likely resume operations at some point in the future, but probably under a different name. This assessment is “based on the fact that NoEscape has become a rebrand of “Avaddon” and given its success in multiple extortion tactics.

