A new MacOS thief has surfaced on the dark web, sparking concern among cybersecurity experts. Operating under a mysterious name, this information stealer has attracted the attention of the security community with its advanced features and capabilities.
Priced at $3,000 per month, MacOS Thief is a sophisticated tool designed to collect sensitive information, posing a significant threat to Mac users.
MacOS Thief Features
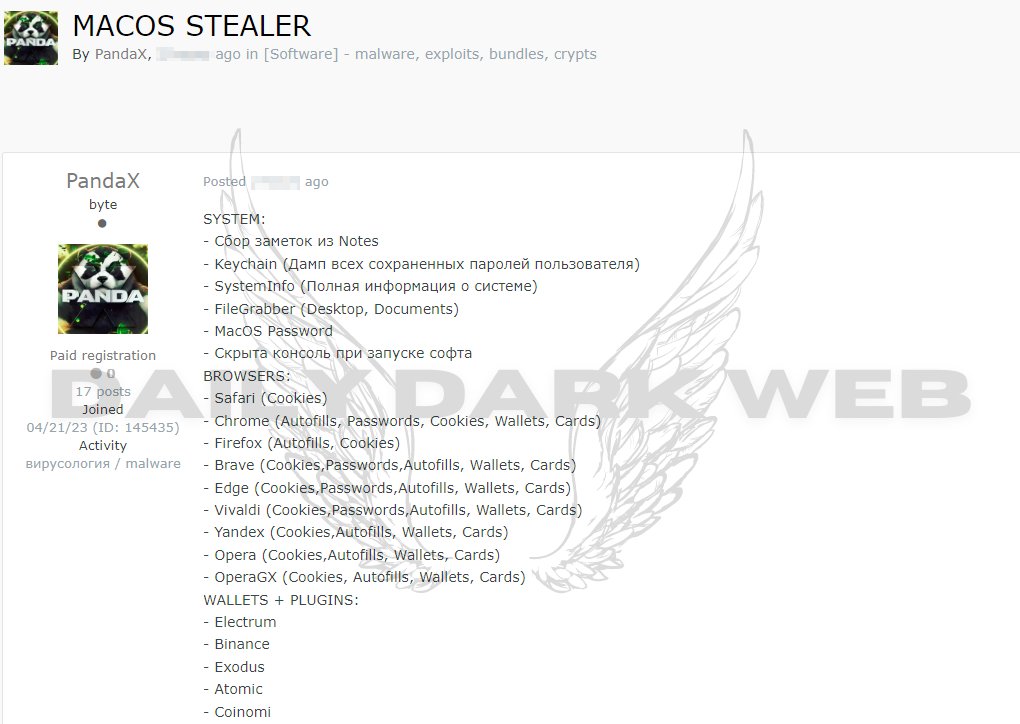
THE MacOS Thief, attributed to the threat actor PANDA and known as PandaX, has an array of powerful features. The threat actor’s post describes its ability to collect notes, keychain files, system information, and MacOS passwords, and use features like FileGrabber and a hidden console when launching the software. This comprehensive range of features allows the thief to access and compromise various aspects of a user’s system.
According to Daily Dark WebtMacOS thief is not limited to a specific browser or platform. It is designed to infiltrate popular browsers like Safari, Chrome, Firefox, Brave, Edge, Vivaldi, Yandex, Opera and OperaGX. Its ability to target a wide range of browsers makes it a versatile threat, posing risks to users in different online environments.
MacOS Information Stealer: Wallets and Plugins
The MacOS thief doesn’t stop at browser data; it also targets cryptocurrency wallets and plugins. With the ability to compromise wallets such as Electrum, Binance, Exodus, Atomic and Coinomi, the thief poses a significant risk to those involved in cryptocurrency transactions.
This is not the first time that a MacOS Information Stealer emerged. Cybersecurity researchers recently identified an improved version of a MacOS information stealer named Atomic. The active improvement of this malware indicates a continued effort by malicious actors to stay ahead of security measures.
The MacOS thief follows a similar modus operandi to its predecessors. Threat actors often repackage pre-cracked applications as PKG files, embedding a Trojan proxy and post-installation script to launch the infection.
Users are tricked into installing compromised apps, which leads to stealth infiltration of their systems. The recent emergence of the MacOS information stealer by several threat actors highlights the adaptability and persistence of threat actors.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only and users take full responsibility for their reliance on it. The Cyber Express assumes no responsibility for the accuracy or consequences of the use of this information.


