Mobile security
WhatsApp, Telegram and Signal clones and mods remain a popular vehicle for malware distribution. Don’t let yourself be fooled.
January 10, 2024
•
,
5 minutes. read

Mobile apps make the world go round. Instant communication services are among the most popular apps on iOS and Android. The American non-profit organization Signal has a estimated 40 million users, with the figure laughrising to 700 million for Telegram, another open source messaging service. Meanwhile, Meta-property WhatsApp is the undisputed world leader with approximately two billion monthly active users.
But their popularity has also attracted the attention of threat actors, eager to find a way to introduce malware to your device. This could end up costing you and even your employer.
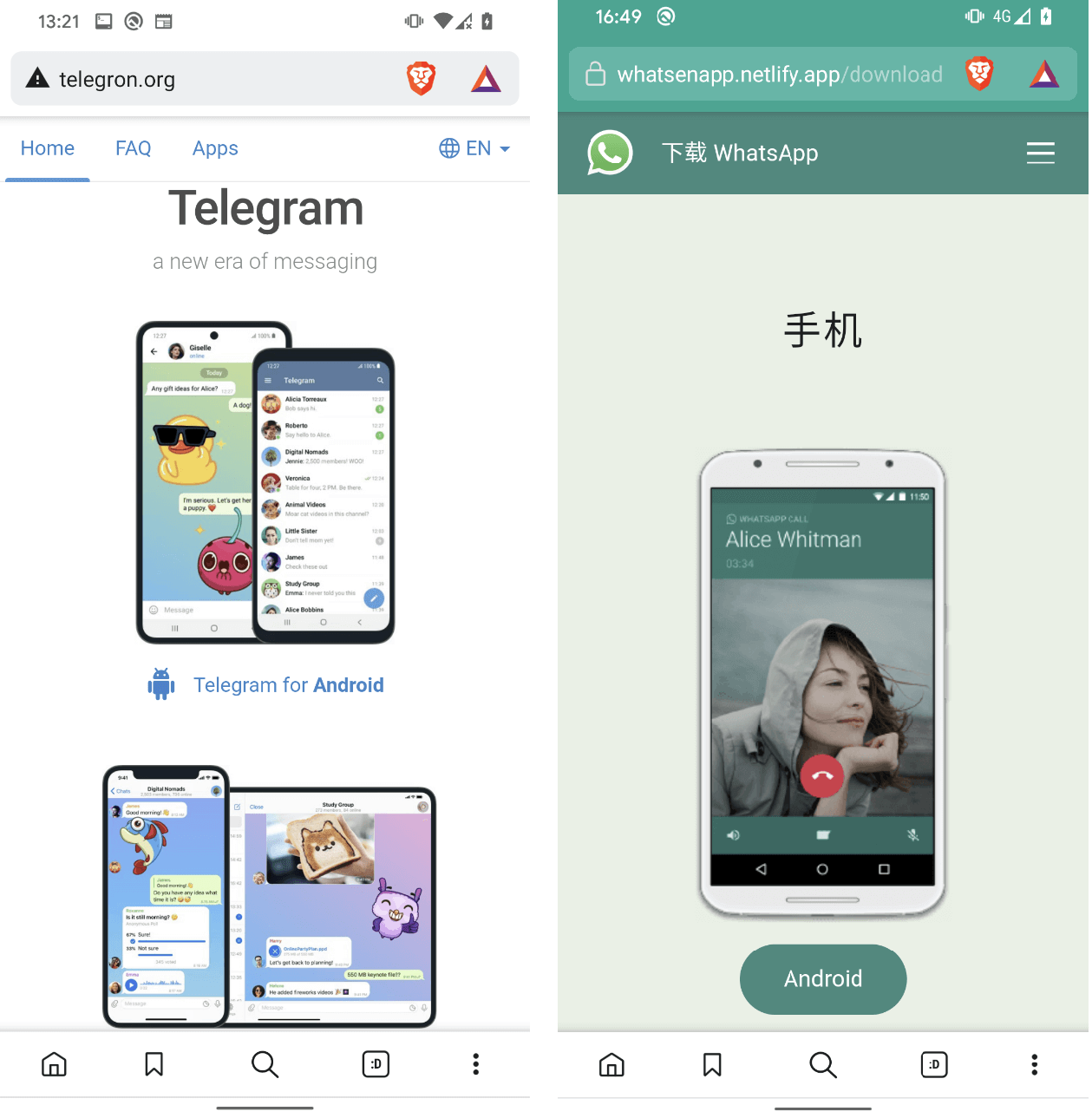
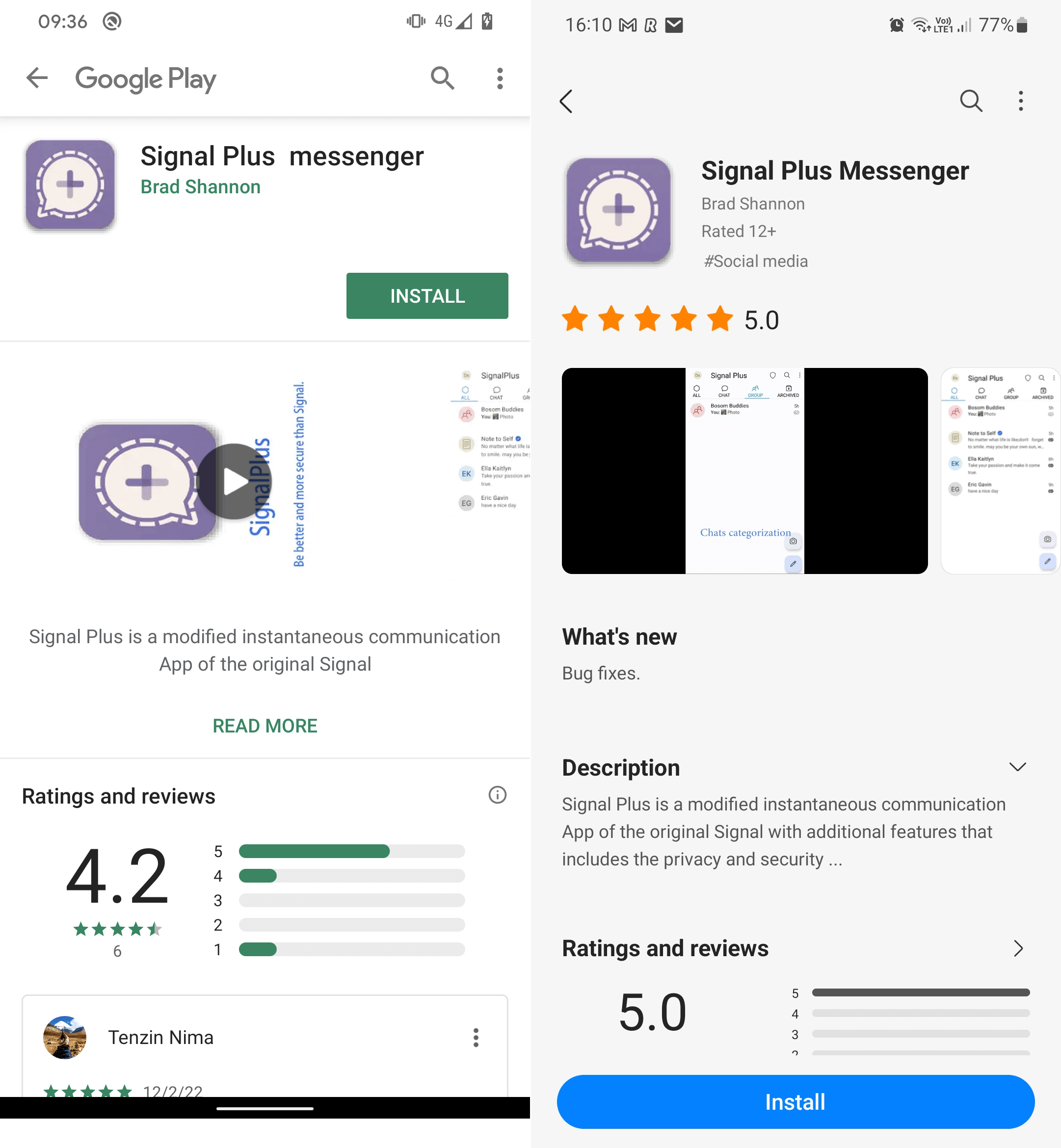
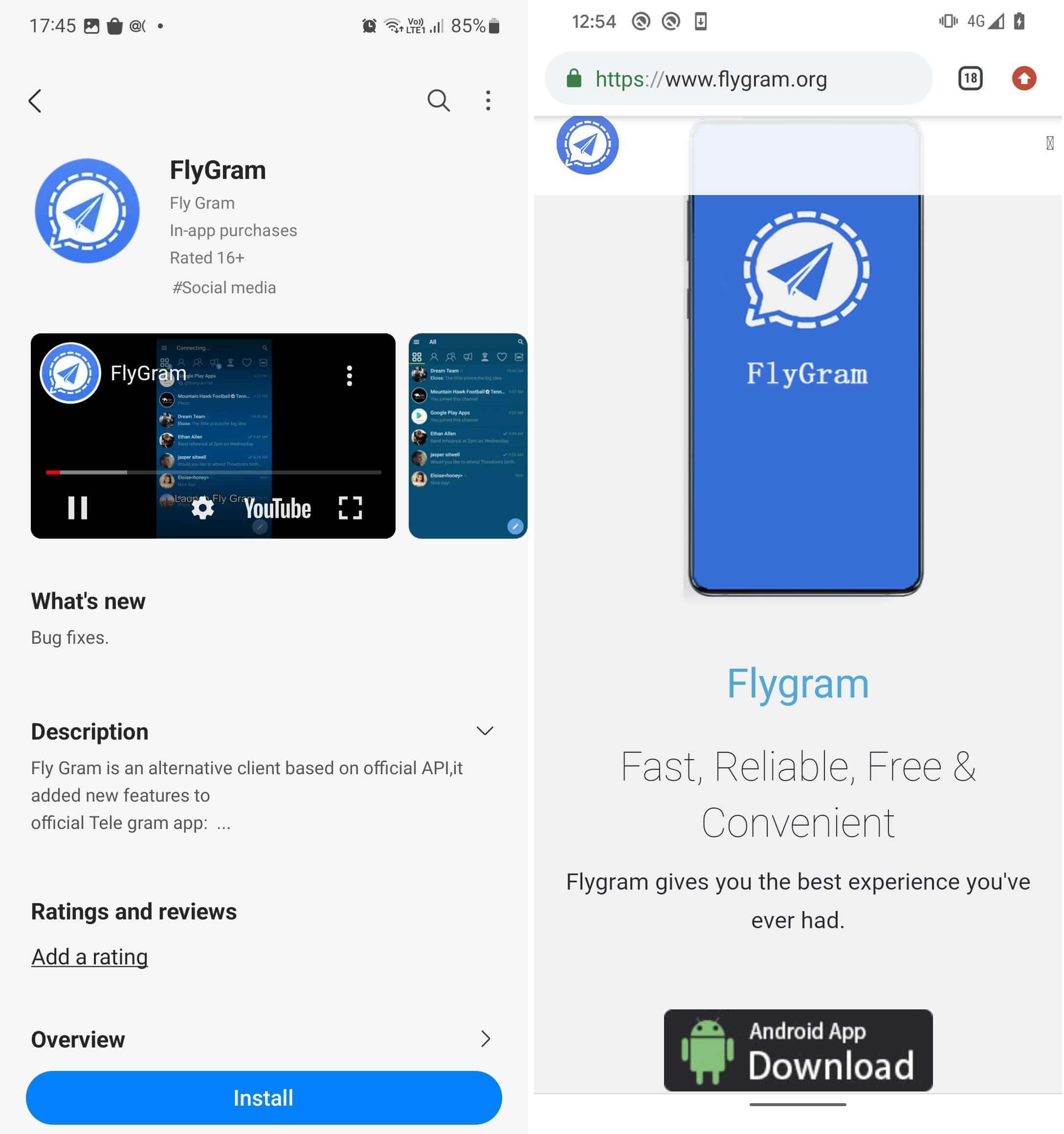
Cyber risks linked to copied malicious applications
Malicious developers have become very good at tricking users into downloading their products. Often, they produce malicious copy apps designed to imitate legitimate apps. They can then spread them via phishing messages via email, SMS, social media or through the communications app itself, directing the victim to a fraudulent page and misleading them into installing what she believes to be an official app. They could also direct users to legitimate-looking fake apps that could occasionally pass through the Google Play Market’s strict screening procedures. Apple’s iOS platform has a lot a more locked ecosystem and it is even less rare for malicious applications to end up there.
Either way, if you download and install a malicious app on your phone, it could expose you or your employer to a range of threats, including:
- theft of sensitive personal data, which could be resold on the dark web to identity fraudsters
- theft of banking/financial information, which could be used to drain funds
- performance issues because malicious apps can change device settings and features and slow it down
- adware that floods the device with unwatched advertisements, making it difficult to use
- spyware designed to listen to your conversations, messages and other information
- ransomware designed to completely lock the device until a fee is paid
- paid services that malware can use secretly, racking up huge bills
- theft of logins for sensitive accounts, which could be sold to scammers
- Corporate cyberattacks designed to steal your credentials or business data, with the aim of accessing sensitive corporate data or deploying ransomware
What ESET saw
These threats have become increasingly prevalent in recent years. Some are opportunistic attacks targeting a broad range of consumers, while others are more targeted. Some of the most notable malicious copy apps observed by ESET include:
- A fake 2021 update campaign which spread across WhatsApp, Signal and other messaging apps via phishing messages claiming that the recipient could get a new color theme for WhatsApp. In reality, WhatsApp pink theme was a malicious Trojan that automatically responded to messages received in WhatsApp and other messaging apps with a malicious link.
- Dozens of websites copied from WhatsApp and Telegram touting malicious messaging apps known as “clippers” – designed to steal or modify the contents of the device’s clipboard. Victims were first lured by Google Ads, leading to fraudulent YouTube channels, which then redirected them to copycat websites. Once installed, the apps were designed to intercept victims’ chat messages in an attempt to steal their sensitive information and cryptocurrency funds.
- Pro-China hackers hid cyberespionage malware known as Android BadBazaar in the legitimate-looking Signal and Telegram apps. Both types of apps were officially vetted and published on Google Play and the Samsung Galaxy Store, before Google/Samsung were informed.

Take precautions against malicious apps
While WhatsApp explicitly prohibited unofficial versions of its application, the open source Telegram encourages third parties developers to create their own Telegram clients. This can make distinguishing between real and fake even more difficult for users. That said, there are several steps you can take to reduce the chances of something malicious being installed on your device.
Here’s a quick checklist:
- Always stick to official Android app stores, as they have rigorous verification processes in place to prevent malicious apps from leaving the platform.
- Always keep your mobile operating system and software on latest version because malware often tries to exploit bugs in older versions.
- Before downloading, always check the developer’s online reputation and app reviews – watching out for mentions of scams.
- Uninstall everything apps you don’t useso it’s easier to track what’s on your device.
- Do not click on links or attachments, especially if they appear in unsolicited social media posts or emails and invite you to download software from third-party sites.
- Avoid clicking on online advertising, in case it is part of a scam designed to lead you to a malicious copycat app.
- Be wary of granting an application permissions that seem unrelated to its functionalitybecause it could be malware trying to access your data.
- Always use a mobile security solution from a reputable provider, as this will help block malicious installations and/or prevent malware from running on your device.
- Consider using biometric logins rather than just passwords on your accounts.
- Never download anything from high-risk sites, such as many adult entertainment or gaming platforms.
How to spot the signs of an imposter app
It’s also helpful to be on the lookout for unusual activity on your device, in case malware sneaks in despite your best efforts. With this in mind, remember:
- If something doesn’t seem right about the app’s name, its description and its “official app” claims, or the developer’s pedigree, there’s a good chance you’re dealing with an impostor app.
- Be aware of persistent pop-up ads, as this may mean that you have installed adware.
- Keep an eye out for unusual icons on your screen that might have been recently installed.
- Be aware of the battery draining faster than usual or other strange behavior
- Keep an eye on your bills and data usage per month; anything excessively high could indicate malicious activity
- Understand that if your device is running slower than usual, it may be due to malware.
Smartphones and tablets are our gateway to the digital world. But it’s a world we must protect from unwanted guests. With these simple steps, you’ll have a much better chance of protecting your finances and personal data.


