When you buy a new smartphone, you’re probably looking for the best value for your money. If you’re looking for a high-end device but don’t want to pay full price, offerings from lesser-known manufacturers will likely be on your shortlist. Indeed, in the fiercely competitive smartphone market, you may be spoiled for choice, as some little-known but high-end competitors can, in many ways, rival the flagships of established tech titans like Apple, Samsung and Google.
On the other hand, while phones targeting those of us who are price conscious don’t break the bank, they lose out when evaluated against criteria like brand recognition, competing telecommunications technologies and, in some cases, global data security and privacy considerations. The prestige (or lack thereof) and pricing policies associated with certain manufacturers also impact public perception – after all, the smartphone has become one of the primary status symbols of our time.
In some ways, even some cutting-edge devices can then be relegated to the mid-range or even budget category. Particularly in the latter case, smartphones are often equipped with older versions of Android and benefit from less or no post-purchase support. They often don’t receive feature or security updates, receive them late or only for a short time, and their manufacturers may even be excluded from the Google Play Store app ecosystem altogether. As shown in several cases where phones have been comes with malware right out of the boxSupply chain security is another reason to worry.
Android multiverse?
With a market share of more than 70 percent, or approximately 3.3 billion active users, Android maintains its position as the world’s leading mobile operating system (OS). However, not everyone is equal in the world of androids. Among full-featured Android smartphones, Samsung leads with a market share of almost 35 percent, while its share of the total smartphone market stands at 20 percent, just behind Apple.
Samsung is leading the pack not only because of its innovative nature and the high quality of its products which offer various options for all budgets. Samsung’s lead is also because its phones benefit from security measures built into Google Play and many of its phones ship with software updates for longer periods than most of its competitors in the ecosystem. fragmented Android. All of this ultimately ensures optimized hardware and software integration and, by extension, improves user experience and security.
Since 2019, new phones from Chinese tech giant Huawei, for example, have been excluded from the Google Play Store. In order to maintain its presence in the global market, the company, which has its own line of high-end smartphone models, has built its own operating system called HarmonyOS. This operating system is largely based on the Android Open-Source Project (AOSP), which is available for free. However, such exclusions from Google Play could have security implications for end users.
Collective security
In addition to security features built into Android, users also benefit from extensive security through the Google Play Store itself and its Play Protect protections enabled by default. This officially sanctioned Android application environment is integrated into phones from smartphone manufacturers that comply with US and European regulations. Store security is supported by Google’s App Defense Alliance, which has been launched in November 2019 and count ESET as a member.
The Google Play Store hosts over 2.6 million appsand almost all could, in theory, have malicious “sleep features” invisible at the time of download or, as was the case with Malware Ahmyth discovered by ESET recently, later receive a malicious update in an incident also highlighted in Google’s report. Thrat Horizons Report August 2023. Where threats are spotted safety conscious stores like the Samsung Galaxy Store and even the Google Play Store, their operators act quickly to remove apps.
As such, Android devices run the risk of several main types of malware. These are banking Trojans, which steal login credentials and can even bypass two-factor authentication (2FA). Another threat is Remote Access Trojans (RATs), which can spy on victims and receive direct commands from attackers to steal money, credentials or data, hijack accounts social networks and record phone calls. There is also Android ransomware that is often spread via malicious links on unsecured websites or in emails and messages. Protecting people from these types of risks is at the heart of the Alliance’s mission.
Safety concerns us all
Most Android devices come with manufacturer skins in addition to the barebones Android version and offer access to Google Play. There are also vendors who have gained a foothold in the market with other AOSP-based operating systems, but their app stores and the apps available there are not approved by the App Defense Alliance.
Using third-party app stores or other unverified places can be tempting because they offer apps you may not find in mainstream stores or offer completely open source (FOSS) alternatives that bypass regional restrictions – or they simply weren’t created by a tech giant you don’t want to share your data with. And although some of these stores are properly regulated and managed by legitimate businessesthere is also hundreds of app stores with less strict or no review processes.
One bottom line emerges: risks from alternative apps and app stores are more likely to impact some phone brands than others, and are a particular concern for those without access to operating system and application environments from Google. (Note: Even people who decide to forgo the protections built into Google Play-supported Android handsets and install apps outside of the official app store can, or soon will, use the store’s real-time scanner to check apps from other sources.)
Uplifting stories abound
There’s no shortage of examples of risks involving third-party app stores and phone makers, including ones you’ve probably never heard of. Let’s review at least a few that have emerged over the years:
- The North East UK Regional Economic and Cybercrime Units issued a warning in 2020, about scammers claiming that specific paid apps – in this case, a fake “TikTokPro” app – could be downloaded “for free” from some third-party app stores. Instead, victims received spyware or adware.
- And, just as there is fake apps, app updates and app stores created to trick victims into downloading malware, similar dangers can come from cheap devices made by B-grade or no-name mobile brands. In 2020, the anti-fraud cabinet Malware detected early submission of fraudulent requests for subscription services on 53,000 Tecno W2 smartphones sold in some African countries.
- Similar threats, embedded in firmware, could be found in devices purchased cheaply on major e-commerce platforms like Ali Baba And Amazon and it’s likely that many budget and ultra-cheap deals come with “additional costs”, such as adware and other nastiness.
- Cheapo phones are not necessarily distributed only in developing countries. In 2020, the US government launched UMX U686CL Android smartphones for low-income users. It later turned out that they had come pre-installed with unremovable malware display unwanted advertisements and download unauthorized applications.
Here there are monsters
ESET Research continues to track mobile threats, including those that target users of software from third-party stores or malware delivered in messages or on websites. Recent threats like Kamran spyware hidden in news app in Pakistan and downloaded directly from a legitimate news site, show just one of many problems with unverified apps. After downloading the app and agreeing to its terms, the app started collecting data such as contacts, calendar events, call logs, location information, device files, SMS messages , pictures, etc.
Chances are you are not from the Gilgit-Baltistan region of Pakistan. However, no matter where you live, you probably use a diversity of apps that help you with banking, provide critical news updates, or simply serve as entertainment. Regardless of the price, brand, or operating system of your chosen phone, you should explore the online world with caution.
Opt for the multi-layered security option
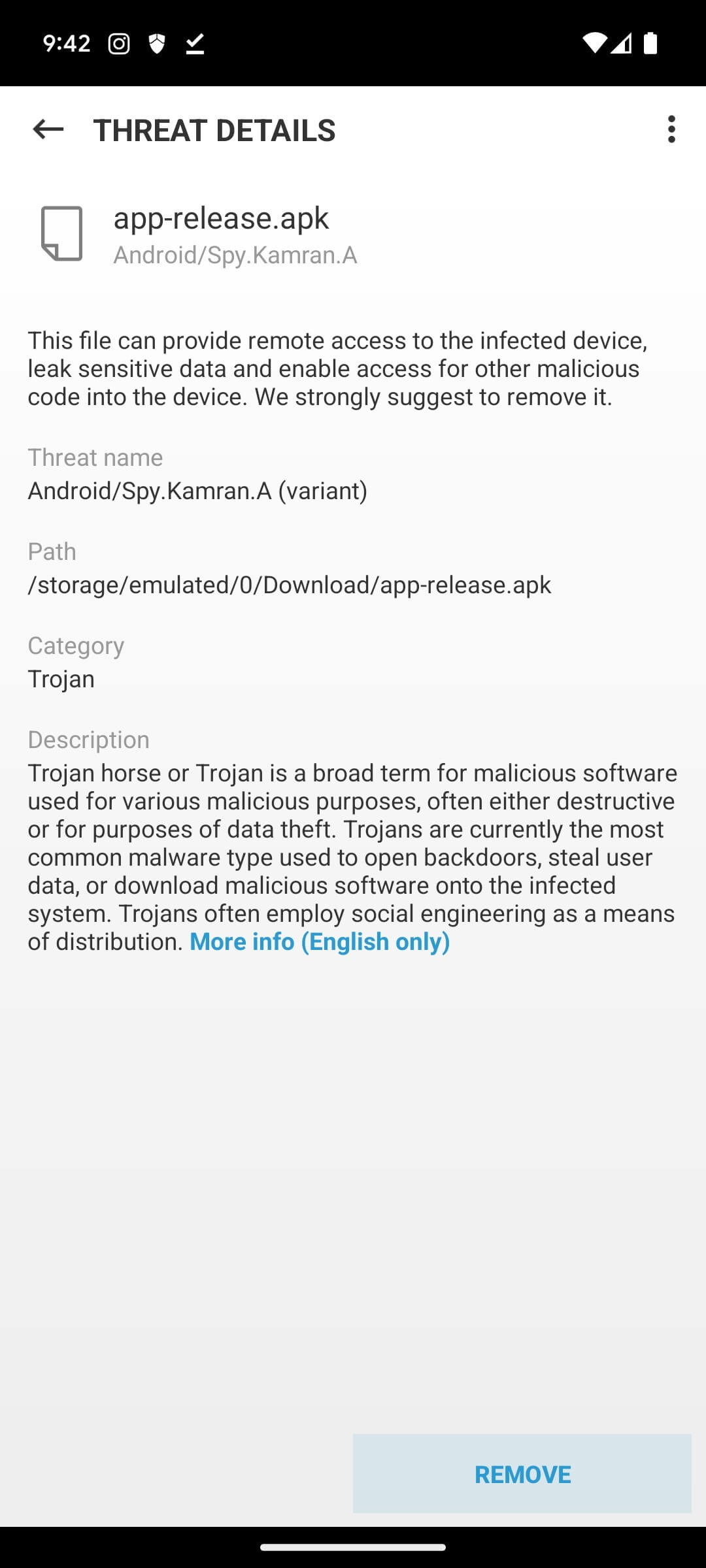
Among other things, the Kamran campaign highlighted the importance of where users get their apps as well as the need for multiple layers of security on mobile devices. Simply, the arsenal of threats and various methods of attack available to criminals – wherever they are – demand protection. For this reason, solutions like ESET Mobile Security (EMS) not only blocks malware as presented in the Kamran case, but also offers comprehensive protection that scans for and blocks potentially dangerous websites and is equipped with payment protection, anti-phishing and proactive anti-theft features.
Spyware such as Kamran and other threats mentioned in this blog, EMS goes a long way in protecting you against these threats. In fact, EMS would have detected Kamran twice – first, via the Anti-Phishing function which would have prevented access to the page and then, thanks to its Anti-Virus module which would have scanned the malicious application before and during the installation process. blocking it as shown in the image below.
Whether out of need or desire for adventure, if you dive into the uncharted waters of budget phones from obscure manufacturers, third-party app stores, and non-mainstream apps, you may face a perilous journey. In such a trip, it is essential to give priority to safety. The easiest thing you can do is download a proven security solution like the multiple award-winning ESET Mobile Security by third-party testers like AV Comparatives and others.


