Ransomware group Rhysida claims to be behind October’s highly disruptive cyberattack on the British Library, leaking a snippet of stolen data.
A low-resolution image shared on its leak site appears to show a handful of passport scans, as well as other documents, some of which display the format of HMRC employment documents.
Rhysida has launched an auction for the stolen data, with the deadline for bids ending just before 08:00 UTC on November 27. The criminals said there would be only one winner who would be the sole recipient of the stolen data. The starting bid was set at 20 Bitcoins, or approximately $745,000.
“With only 7 days left, take the opportunity to bid on exclusive, unique and impressive data,” Rhysida’s message on its website reads. “Open your wallets and be ready to buy exclusive data. We only sell to one hand, no resale, you will be the sole owner.”
Needless to say, no recipient has any way of knowing this and if Rhysida is indeed behind the attack, he can keep unlimited backups.
The register contacted the British Library for comment, but they did not respond.
The British Library has confirmed a major computer failure at the end of October, due to a cybersecurity problem. He confirmed the incident was ransomware in nature on November 14, but Rhysida’s claim only came this morning, Monday, November 20.
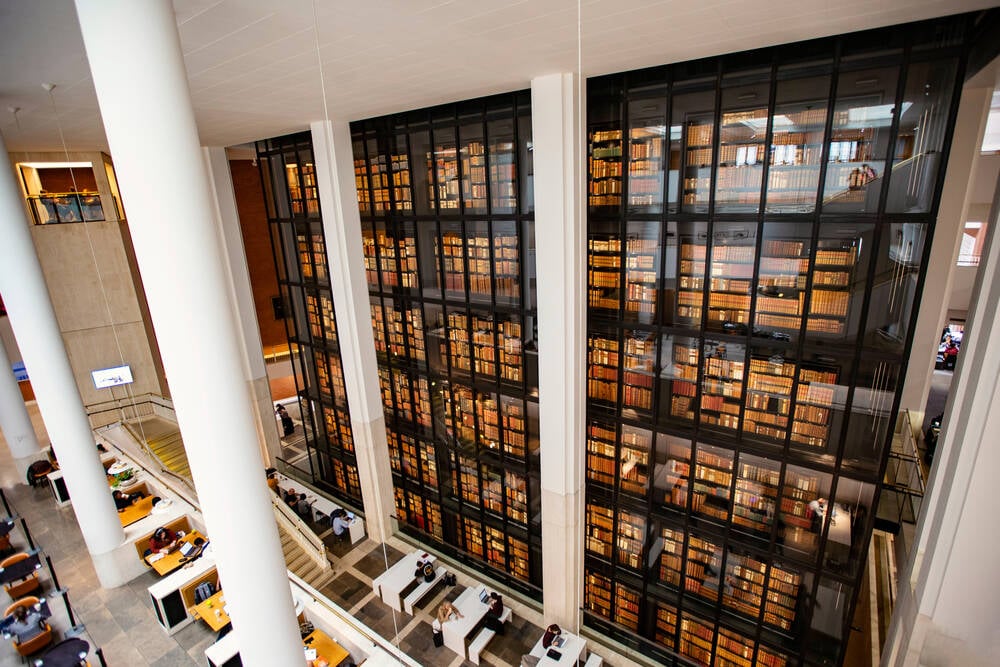
The disruption caused by the attack remains significant. When the attack was first confirmed, the famous red brick venue at St Pancras Library in London was operating cash only while electronic payments were in decline. Wireless internet connectivity for visitors was also not available and order collection facilities were limited.
The website remains unavailable at the time of writing, as it has for weeks.
Regular updates were provided via the library’s X account and a separate website, with services still experiencing outages and disruptions.
Responding to a question via social media regarding a potential data theft, the British Library said on November 15 that it was still unaware of the scale of the attack.
“We can currently only confirm which services are still available, but we are working to understand and resolve the situation as quickly as possible, as well as to restore our other services,” it says. said.
“We will share updates on how this may affect our users as soon as possible. We are truly sorry for any inconvenience this has caused.”
Rhysida’s claims that he was behind the attack come weeks after the British Library first confirmed the incident, and a week after it was confirmed to be of ransomware – an indication that negotiations may have failed.
“Ransomware attacks naturally come with a negotiation phase immediately after the attack, which can take time to find the right balance,” said Jake Moore, Global Cybersecurity Advisor at ESET. The register.
“If the victim must consider payments, this difficult period may take days before more details are released. Victim parties often keep most of their attacks secret, but the criminal group will quickly want to claim responsibility.
“When a group allows some time to claim responsibility for its crimes, it can usually mean that such negotiations have gone back and forth to get the right price for both sides. Considered a model (of ransomware as a service), Rhysida is likely to I did not receive the ransom they finally demanded and are now pushing back the next phase of the attack by threatening to release the data.
Rhysida wakes up the authorities
The US Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory on November 15 to raise awareness of the ransomware strain that has been opportunistically targeting organizations since May 2023.
Primarily targeting the education, healthcare, manufacturing, IT, and government sectors, Rhysida is known to access victims via old vulnerabilities such as Zero Connectionand using phishing and stolen credentials to authenticate to organizations’ VPNs that are missing M.F.A. by default.
Some security researchers have related Rhysida’s activity with groups like Vice Society, noting similarities in the tactics and techniques of Rhysida-related attacks.
Rhysida is considered a ransomware-as-a-service (RaaS) group in its own right, and Vice Society – is believed to be behind major attacks like that of Los Angeles Unified School District – may be using his kit, the researchers theorized.
It operates on a double extortion model, as the British Library attack appears to demonstrate, and the group tends to use land subsistence techniques – using pre-loaded admin tools to blend in with the traffic typical network. ®