Part of my series on Automation of cybersecurity measures. S3. KMS. Deploy a static website. THE Coded.
Free content on Cybersecurity Jobs | Register at Broadcast list
In the last article I wrote a summary of some of the reasons why I don’t use step functions after creating a base container image for my Lambda functions.
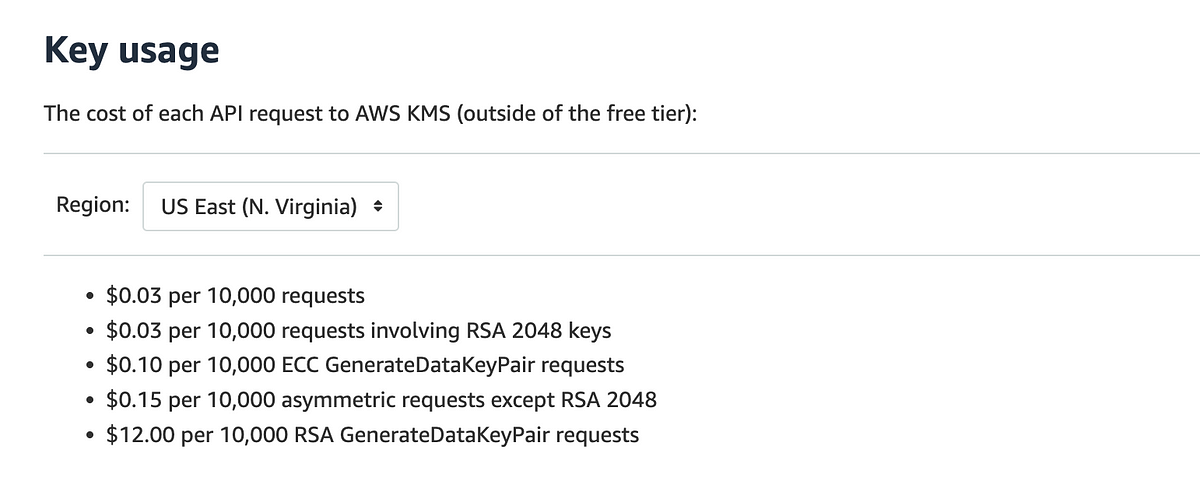
In this article I want to review the KMS key I use for the S3 bucket I use to host my website. As you may recall, I was thinking about the pros and cons of using a KMS key since it is for a public website. By encrypting everything, you can check some compliance boxes. This could potentially contribute to the integrity of the website’s content, even if the content is public.
Then I was talking to a customer who had deleted KMS keys from their S3 buckets due to cost and remembered that AWS had offered a new option for encrypting S3 buckets a while ago. I thought I should try it and write about it. My usage is tiny compared to many companies so I’m not sure it will make a difference in my costs, but if it’s ultimately cheaper and since it’s already public data anyway, I might as well use this option.
How is an S3 bucket KMS key different?
Normally, Amazon S3 makes a call to AWS KMS whenever a query is made on a KMS-encrypted object.
When you create an AWS S3 bucket key, AWS contacts KMS to create a short-lived key that is used for encryption operations and is stored in S3 while in use. This local key is used throughout its life to perform encryption operations, reduce the number of round trips to KMS.
This allows AWS to reduce your costs for these key types.