On March 2, 2021, Microsoft accused a Chinese group APT, called Hafnium, of having compromised 30,000 Exchange servers. They announced four security vulnerabilities, called 0-day, which refers to the fact that attackers had a reliable way to exploit the vulnerability for which there was no patch. In case your organization doesn’t go into full panic mode, GO TRIGGE THE FIRE ALARM! IT IS SERIOUS!
Tom Burt, vice president of security and customer trust at Microsoft, published a blog post about Hafnium: New cyberattacks at the nation-state level. Microsoft describes Hafnium as “primarily targeting entities in the United States with the aim of exfiltrating information from a number of industry sectors, including infectious disease researchers, law firms, higher education institutions , defense contractors, policy think tanks and NGOs.” According to my favorite APT cross-reference table, maintained by Florian Roth (Twitter: @Cyb3rOps) Hafnium is also called by Symantec under the name Ant. (They chose this name because one of the common webshells used for post-exploitation was regularly hit by a web browser using the “antSword/v2.1” user agent. AntSword (中国蚁剑) and ChinaChopper (中国菜刀) are popular webshells used by Chinese attackers for many years.
FireEye says there is no reason to believe the activity is limited to a single threat actor and refers to the attack groups like UNC2639, UNC2640, UNC2643.
FireEye associates UNC2639 with activity from IP addresses 165.232.154.116 and 182.18.152.105, both active at the time of Microsoft’s announcement (March 2 and 3).
FireEye associates UNC2640 with activity involving “web shell” files named “help.aspx” (MD5 4b3039cf227c611c45d2242d1228a121) and “iisstart.aspx” (MD5 0fd9bffa49c76ee12e51e3b8ae0609ac)
FireEye associates UNC2643 with the deployment of a Cobalt Strike Beacon (MD5 79eb217578bed4c250803bd573b10151) and the IP addresses 89.34.111.11 and 86.105.18.116.
FireEye claims to have started observing this activity in January, which matches Microsoft’s reports that they were informed of this activity by security firm Volexity in January. However, the DEVCORE research team deserves credit for attempting to exploit marketing of the bug by calling the attack “Proxy connection” and create a sexy web page and logo for the attack, a la HeartBleed. Luckily, it didn’t really catch on, but their timeline is still very interesting. They found the first bug on December 10, 2020 and the second on December 30, 2020 and reported both to Microsoft on 05JAN2021 (as tweeted by their Taiwanese researcher, Tsaï Orange.)
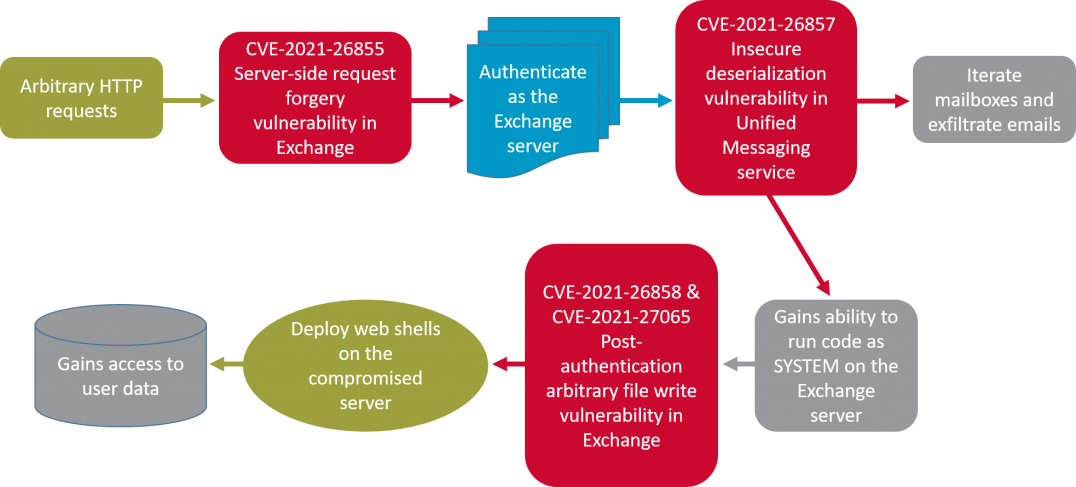
Symantec specifies that the actor they call Ant (and Microsoft calls Hafnium) is definitely no longer the only attacker using these vulnerabilities. Diagram of the Symantec attack Is usefull:
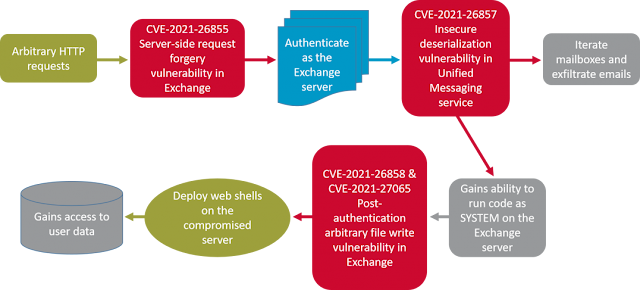 |
| Symantec Attack Flowchart |
Brian Krebs interviewed several researchers about the attack, including Steven Adair, who says his company, Volexity, has noticed the bug since January 6, 2021. See Krebs on security: “At least 30,000 US organizations newly hacked via flaws in Microsoft email software. »
As Krebs and others have since pointed out, while 30,000 U.S.-based organizations were known to be victims of Hafnium/Ant, now that the vulnerability is known, attacks have reached astronomical numbers. Why is it a problem? Companies most likely to operate their own unpatched email servers are also least likely to be informed enough to apply the patches.
Both Forbes And CABLE Now let’s say that hundreds of thousands of servers were compromised and the number of compromises at any given time was increasing by “thousands per hour”.
What to do? PATCH! (But it may be too late…)
Obviously, the most important thing to do is to apply Microsoft’s patches. However, it is VERY IMPORTANT TO UNDERSTAND that you may already be compromised. Patching DOES NOT make you “unhacked!” Patch, but also follow CISA’s advice to determine if you’re already hacked.
The vulnerabilities are listed here, each linked to the Microsoft security alert associated with the CVE.
What do you think are the chances that they suddenly became aware of the patches on MARCH 02, 2021?
It is highly likely, in this author’s opinion, that MOST of the Exchange servers accessible on the Internet have been compromised. How to test to see if you are one of them? Continue reading…
WHAT TO DO? SEE IF YOU ARE HACKED!
The CyberSecurity & Infrastructure Security Agency, CISA, part of the Department of Homeland Security, has provided comprehensive information on how to detect the attack, including an interesting guide on how to use FTK Imager to capture the memory of your Exchange server and where to look. proof of being compromised.
Please carefully review their recommendations found as Alert AA21-062A.
Many of their indicators come from Volexity, which also shares a video explaining the attack in its 02MAR2021 blog post, “Operation Exchange Marauder. “It should be noted that none of FireEye’s IP addresses are in this list.
In addition to the CISA guidance, Microsoft has released a script that can be run on your Exchange server to look for signs of compromise. Their scenario is described in their Hafnium targeting Exchange servers blog post, but a direct link to the script is:
https://github.com/microsoft/CSS-Exchange/tree/main/Security
This script scans HttpProxy logs, Exchange logs, and Windows application event logs for signs of exploitation. Let’s hope the bad guys haven’t deleted the logs!