A network component of Garrett Metal Detectors contains a number of security vulnerabilities that could allow remote attackers to bypass authentication requirements, tamper with metal detector configurations, and even execute arbitrary code.
In a disclosure published last week, Cisco Talos said an attacker could use this module to remotely monitor a metal detector’s statistics, such as whether the alarm was triggered or how many visitors passed through. “They could also modify device configurations, such as changing the sensitivity level, potentially posing a security risk to users of these metal detectors.”
Matt Wiseman, a security researcher at Talos, was credited with discovering and reporting these vulnerabilities on August 17, 2021. A patch was released by the vendor on December 13, 2021.
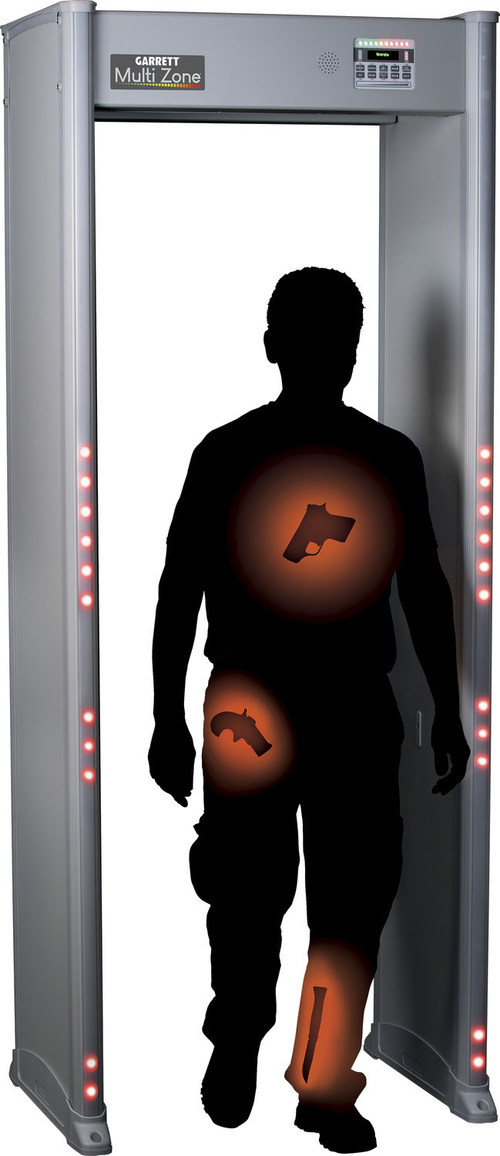
- The Garrett iC module, which allows metal detectors like the Garrett PD 6500i and Garrett MZ 6100 to communicate with a computer over the network, wired or wireless, contains these defects. Customers can control and monitor their devices in real time from a remote location.
- Below is a list of security vulnerabilities –
- CVE-2021-21901 (CVSS score: 9.8), CVE-2021-21903 (CVSS score: 9.8), CVE-2021-21905 and CVE-2021-21906 (CVSS scores: 8.2) – Vulnerabilities of Stack-based buffer overflow that can be triggered by sending malicious packets to the device
- Authentication bypass vulnerability resulting from a race condition that can be triggered by sending a sequence of requests (CVE-2021-21902) (CVSS: 7.5)
- CVE-2021-21904 (CVSS score: 9.1), CVE-2021-21907 (CVSS score: 4.9), CVE-2021-21908 and CVE-2021-21909 (CVSS scores: 6.5) – Vulnerabilities of directory traversal which could be exploited by sending special commands
Successful exploitation of the aforementioned bugs in iC Module CMA version 5.0 could allow an attacker to hijack an authenticated user’s session, read, write, or delete arbitrary files on the device, and worse, execute code remotely.
Users are strongly advised to update to the latest firmware version as soon as possible due to the severity of the security vulnerabilities.