~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~ ~~~~~~
⚙️ Part of my series on Automation of cybersecurity measures. THE Coded.
🔒 Related Stories: AWS Security | Application security
💻 Free content on Cybersecurity Jobs | ✉️ Register for Broadcast list
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~ ~~~~~~
I wrote about the potential injection of resources into CloudFormation stacks in the last article:
The reason I’m thinking about imports that led to drift detection, which led to cases where it didn’t work in the previous post, is that I need to find a solution with my AWS Organization import when doing my very first deployment to a new account.
I have a single container that can be used to deploy almost anything:
I want to modify the initial deployment in a new account to use this container, so I will create a configuration for it in my configuration repository. I wrote about these repositories here:
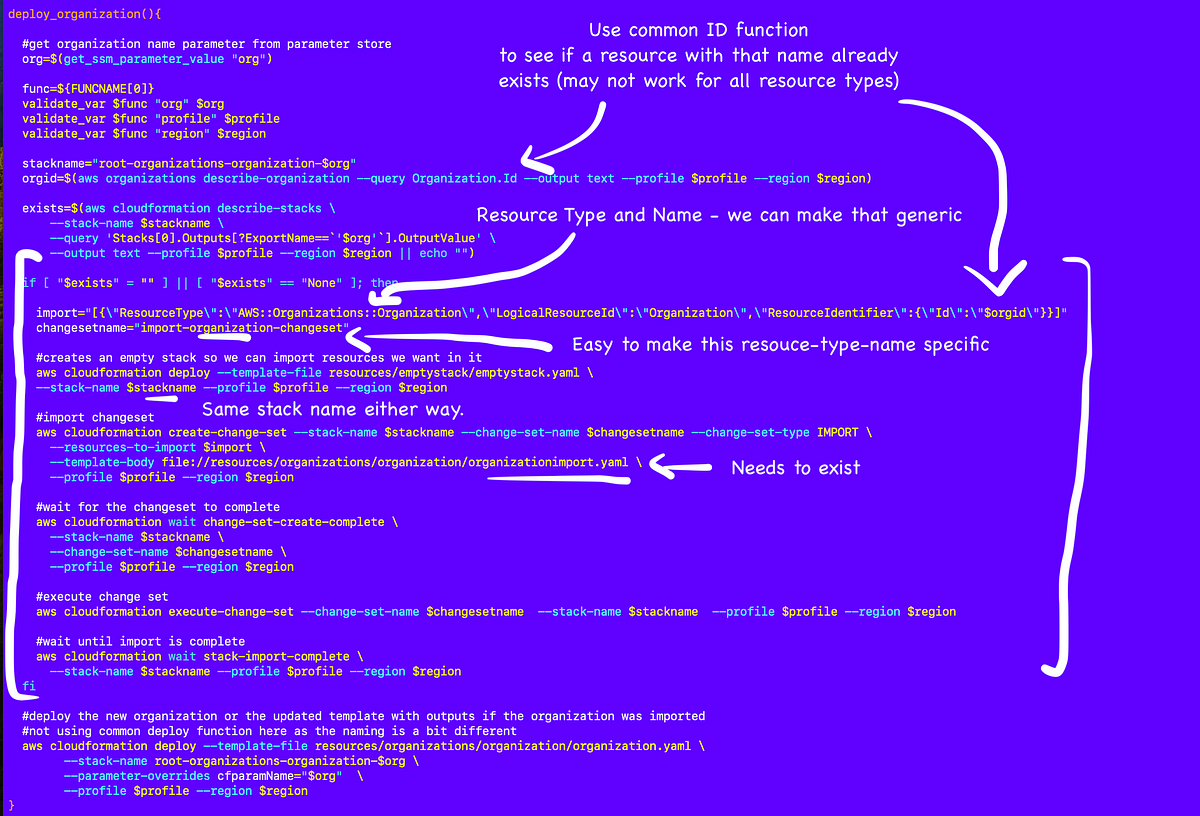
I was about to do it when I realized I had forgotten one thing. The AWS Organizations deployment imports the resource if it already exists, otherwise it updates it.
So that brought me back to thinking about something I was thinking about earlier. Can I make this import generic so that it can be used for all resource types?
Probably. With a few caveats.