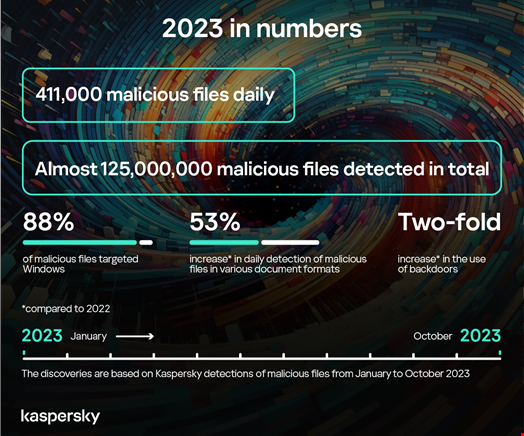
Cybercriminals distributed an average of 411,000 malicious files each day in 2023, an increase of 3% from the previous year, according to Kaspersky.
The firm Safety Bulletin: Report on statistics for the yearreleased on December 14, 2023, showed that certain types of threats have also intensified.
An example is the use of malicious office files (Microsoft Office, PDF…) to spread malware. Of the 125 million files detected by Kaspersky in 2023, 24,000 were such documents, an increase of 53% compared to 2022.
“This growth could be linked to an increase in attacks using phishing PDF files, designed to steal data from potential victims,” the report said.
Rise in the use of backdoors
Microsoft Windows remains the top target for cyberattacks, accounting for 88% of all malware-containing data detected daily. The firm has, however, observed some interesting samples of macOS malware, notably in France, China and Italy.
Many malicious files targeting macOS systems were disguised as adware.
The most common type of malware remains Trojans, with a notable increase in the use of backdoors, growing from 15,000 files detected per day in 2022 to 40,000 in 2023.
“Backdoors stand out as one of the most dangerous types of Trojans, providing attackers with remote control over a victim’s system to perform tasks such as sending, receiving, executing and deletion of files, as well as collection of confidential data and recording of computer activity. » Kaspersky researchers wrote.
Magniber, WannaCry and Stop/Djvu were among the ten Trojan families most detected by Kaspersky.
Bangladesh, Yemen and Taiwan were the three countries most targeted by ransomware Trojans.
Microsoft Office vulnerabilities favored
Cybercriminals have particularly favored vulnerabilities in Microsoft Office services. They accounted for 69.10% of all exploited vulnerabilities.
“The reporting period was marked by a number of dangerous vulnerabilities in business applications, such as CVE-2023-34362, CVE-2023-35036 And CVE-2023-35708 in MOVEit Transfer or CVE-2023-23397 in Microsoft Outlook,” the researchers noted.
Read more: MOVEit Exploitation Fallout Generates Record Ransomware Attacks
Most prolific LockBit, BlackCat and Clop
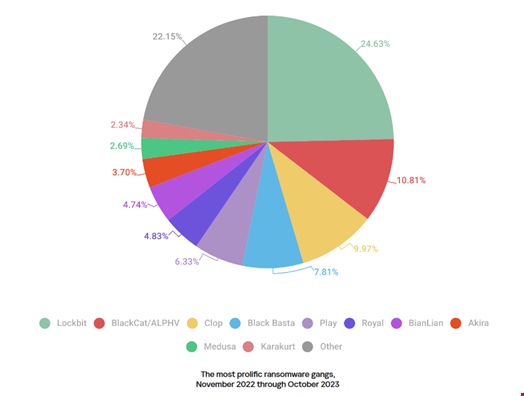
According to Kaspersky telemetry, the most prolific ransomware group was LockBit, which claimed a 24.63% share of the total victims published across all of the groups’ data leak sites.
LockBit was followed by ALPHV/BlackCat (10.81%) and Clop (9.97%).
Read more: ALPHV second largest ransomware strain before reported downtime
Vladimir Kuskov, head of anti-malware research at Kaspersky, said: “Adversaries continue to develop new malware, techniques and methods to attack organizations and individuals. The number of reported vulnerabilities also increases every year, and threat actors, including ransomware gangs, use them without hesitation.
“In addition, the barriers to entry into cybercrime are now lowered due to the proliferation of AI, which attackers use, for example, to create phishing messages containing more convincing text. Nowadays, it is essential for both large organizations and every regular user to adopt reliable security solutions.
All figures in The report, which covers the period from November 2022 to October 2023, come from the global cloud service Kaspersky Security Network (KSN). The data was obtained from users who had consented to it being sent to KSN.


