ACM.380 Accessing a private ECR repository and using the container to deploy resources to the remote account
Part of my series on Automation of cybersecurity measures. AWS Organizations. I AM. Deploy a static website. THE Coded.
Free content on Cybersecurity Jobs | Register at Broadcast list
In the last article I realized that STS simply won’t work between accounts in a private network with VPC endpoints (as far as I know at this point.)
I want test deploying resources to an external AWS account and I can do it in a public VPC but I need to access my private repository.
Anyone I authorize to access this private repository also needs authorization to access the KMS key.
I don’t want to grant cross-account access to this key, so for now I’m going to use my local role which has access to the private repository but from a public VPC.
This wouldn’t work if I was required to access the repository only from specified VPC endpoints, which I hope to add later. But it’s not here at the moment, so I’ll use it for now.
The reason I couldn’t access the ECR repository earlier is because I was trying to retrieve the image with the remote account. This account does not have access to the repository. But my SandboxAdmin does.
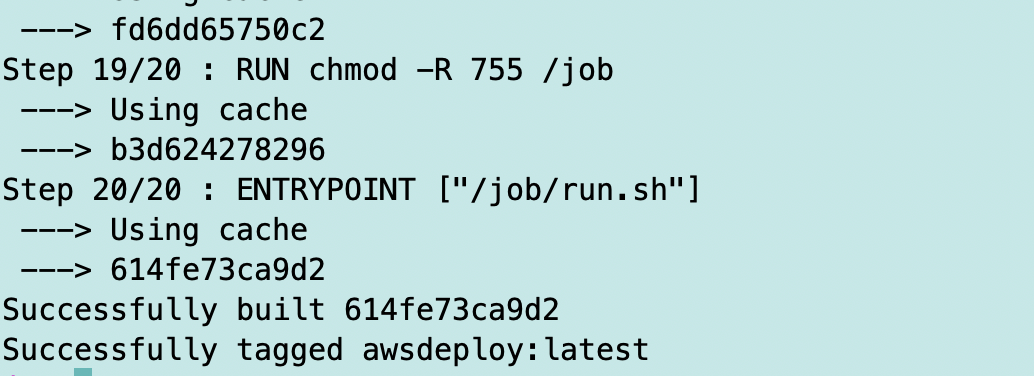
So I need to pull the image with SandboxAdmin first and then assume the role in the other account to run the deployment.
The other thing I realized was that I was using my remote account number in the pull request. Oops.
So now that we know we can make this work in a public network, I’m going to use the host that I deployed on the public network to achieve this.
Again, it’s not ideal but for now I want to keep moving forward. If I was at a large company and really wanted to address this issue, I would talk to my AWS…