~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~ ~~~~~~
⚙️ Part of my series on Automation of cybersecurity measures. THE Coded.
🔒 Related Stories: AWS Security | Application security | Batch jobs
💻 Free content on Cybersecurity Jobs | ✉️ Register for Broadcast list
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~ ~~~~~~
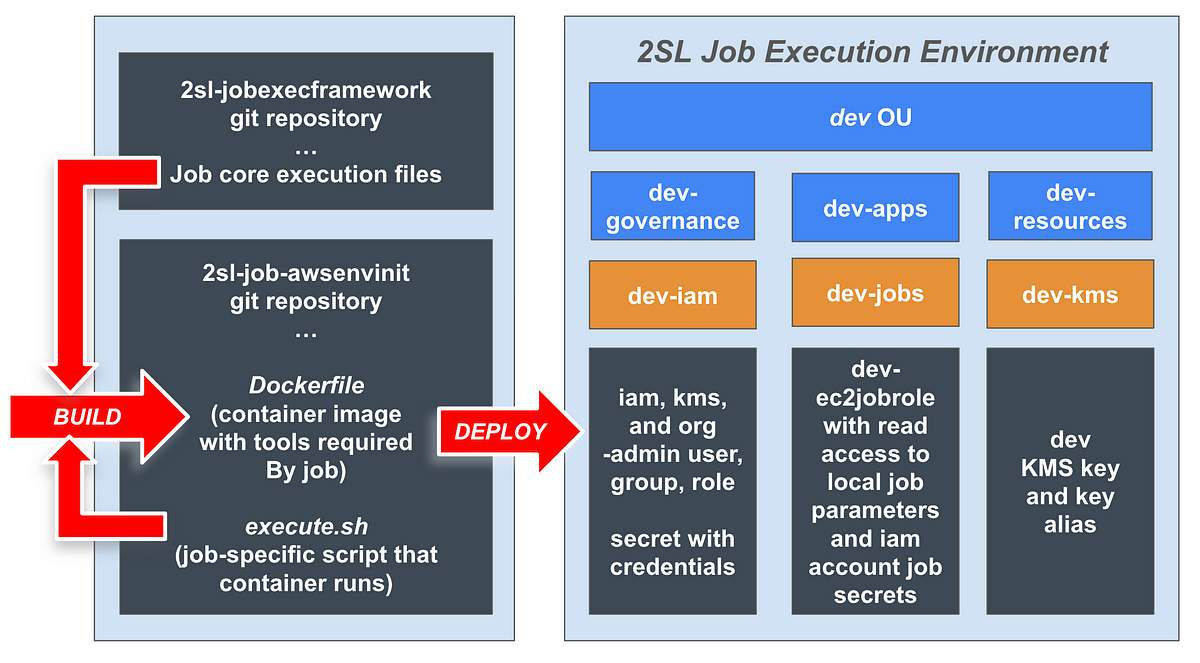
In the last article, I explained what a task execution environment is for the 2nd Sight Lab task execution framework.
In the next series of articles, I will build this environment piece by piece. At the end, you will have a job that you can run using the 2nd Sight Lab Job Execution Framework to create a new environment for future jobs.
The difference with this task is that we haven’t created our task execution environment yet, so the task will pull credentials from CloudShell. As mentioned, I don’t recommend using CloudShell for reasons described in a previous article, but I don’t want to deploy secrets with AWS developer credentials or access keys in the root management account of our organization.
Aside from the difference in where the credentials come from, the job will function essentially the same as a job run through a test script from the runtime environment we create.
Create a new repository
The first step is to create a repository for our work and create a container that can run the work.
I’ve explained the separate repositories used by the framework here:
We will create a new repository for this work named 2sl-job-awsenvinit.