ACM.401 Overcoming CloudFormation Limitations for Dynamic SCPs and Delegated Admin Challenges with IAM Permissions
Part of my series on Automation of cybersecurity measures. AWS Organizations. I AM. Deploy a static website. THE Coded.
Free content on Cybersecurity Jobs | Register at Broadcast list
In the last article I took a break to write about the code I use to generate code — without generative AI 🙂 This was my 400th article in this particular series and I thought it was pretty cool and a special article for this monumental issue. .
My goal throughout this series has been to minimize the time I have to spend writing code to deploy new resources and I’m getting closer and closer to that goal, while implementing governed infrastructure to help limit configuration errors and unauthorized access. Ultimately, I want to report on my own infrastructure and configurations.
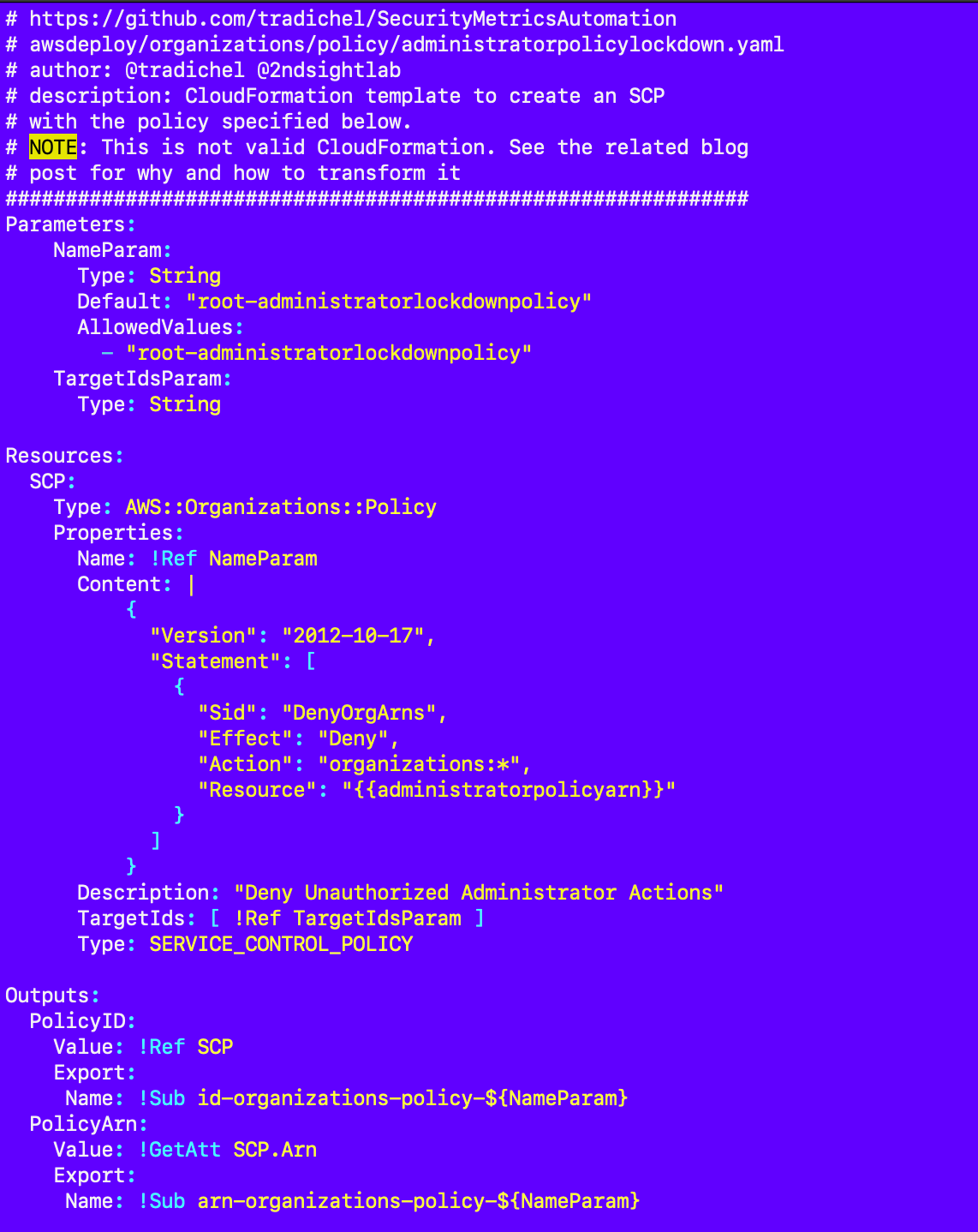
Before this, I wrote about the conundrum of limiting access to modify a single service control policy using the SCP itself or predicting the ARN – and it doesn’t seem like you can do neither.
In this article, my goal is to solve this problem. Type of. I want to write a script that dynamically writes a template for this policy that will run in any account. This won’t work if I have to hardcode a policy ARN.
Since I am unable to create dynamic SCPs using CloudFormation, I will need to dynamically write the file before CloudFormation accesses it.
Also note that if you grant someone delegated administrator access for organizations, there are many opportunities for them to bypass the controls on SCPS that you have applied at the root. Think about all the ways they can create a new user or assume a role or change SCPs or policies to…